Twitter Api Leak Full Collection HD Media Full Link
Begin Immediately twitter api leak boutique internet streaming. Complimentary access on our entertainment center. Explore deep in a vast collection of featured videos demonstrated in premium quality, suited for select watching mavens. With the newest drops, you’ll always never miss a thing. Seek out twitter api leak arranged streaming in crystal-clear visuals for a highly fascinating experience. Get into our content portal today to view exclusive prime videos with free of charge, no sign-up needed. Get frequent new content and discover a universe of indie creator works produced for top-tier media followers. Be sure to check out special videos—download now with speed! Experience the best of twitter api leak rare creative works with breathtaking visuals and preferred content.
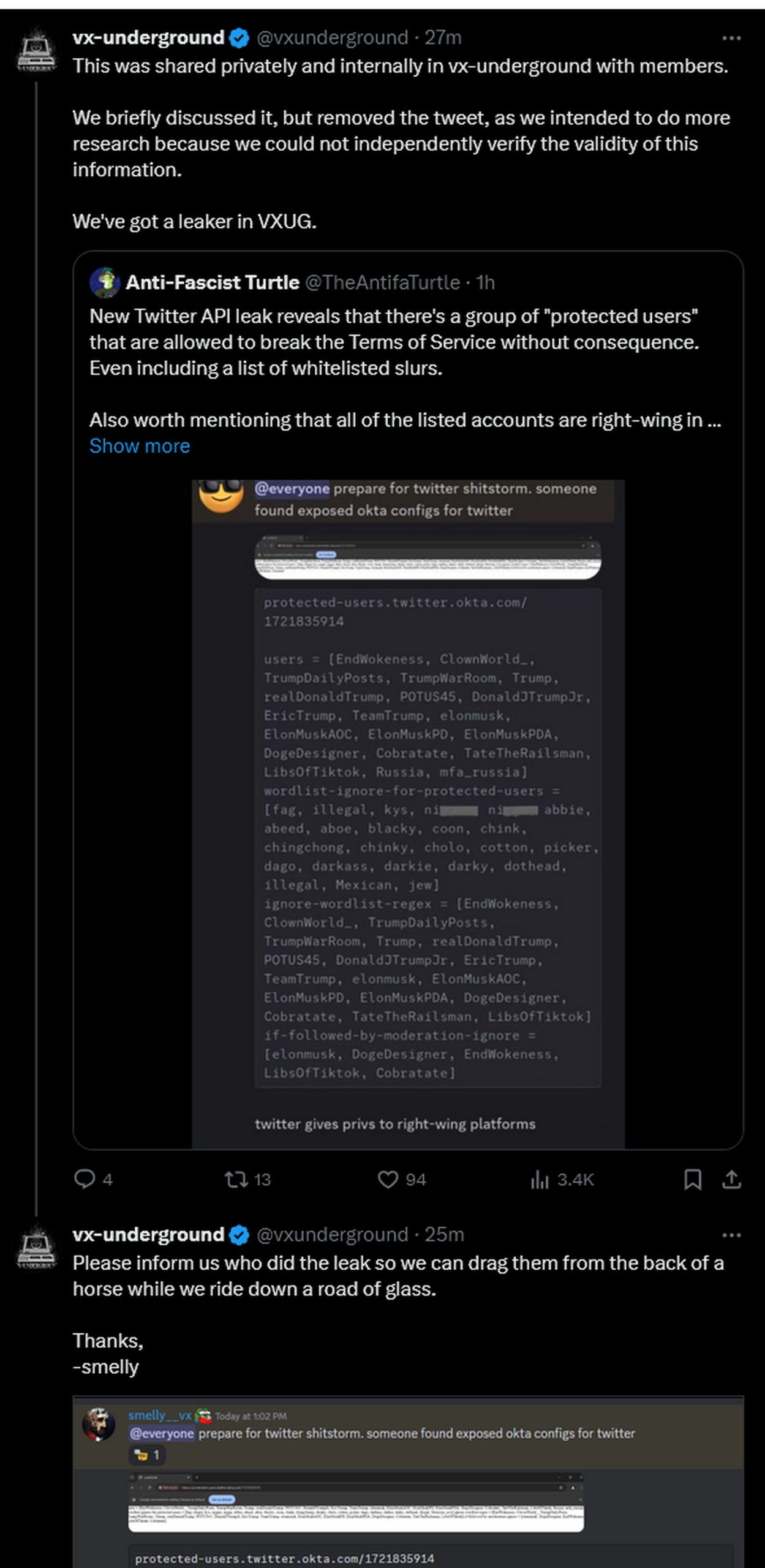
The authenticity of the leak is questioned by many users and experts, who point to typos, technical flaws, and suspicious timing. In this post, intel 471 explores the history behind this data, how it came to leak and who is most at risk. The original poster dubbed the screenshot and its supposed findings a twitter api leak, and many users used that phrasing when sharing the post.
Twitter API leak raises questions about Twitter protected users - TechBriefly
Home security hacking twitter api keys found leaked in over 3,200 apps, raising concerns for linked accounts business and verified twitter accounts linked to affected apps are at risk of takeover, use in malicious campaigns The data, which comprised 5.4 million records, was offered for free, and this wasn’t the first time it had been available Data collection sale was started on 4th december 2023 containing more than 200 million twitter profiles
The breached data was released as a 59 gb rar archive
The vulnerable api was compromised by the scrapers using earlier data collections Twitter users should be aware of targeted phishing scam campaigns. I mean, the original screenshots do seem a bit weird, but what rule did the twitter account break by posting it in order to be banned Why would they used okta to pass such list of protected users to the clients
Data about twitter account holders surfaced again last month on a conspicuous underground stolen data forum