Sha_griff Onlyfans Full Library Video/Photo Instant
Begin Your Journey sha_griff onlyfans world-class live feed. Gratis access on our viewing hub. Submerge yourself in a vast collection of featured videos featured in HDR quality, essential for high-quality viewing viewers. With current media, you’ll always stay updated. Watch sha_griff onlyfans personalized streaming in impressive definition for a deeply engaging spectacle. Get into our video library today to observe unique top-tier videos with completely free, access without subscription. Get fresh content often and investigate a universe of original artist media designed for high-quality media admirers. Don't pass up uncommon recordings—download fast now! Witness the ultimate sha_griff onlyfans special maker videos with breathtaking visuals and unique suggestions.
Web self registration ussd self registration assisted enrolmentfrequently asked questions The sha (secure hash algorithm) family currently designates a family of six different hash functions We are a volunteer organization led by parents and guardians of sacred heart academy students
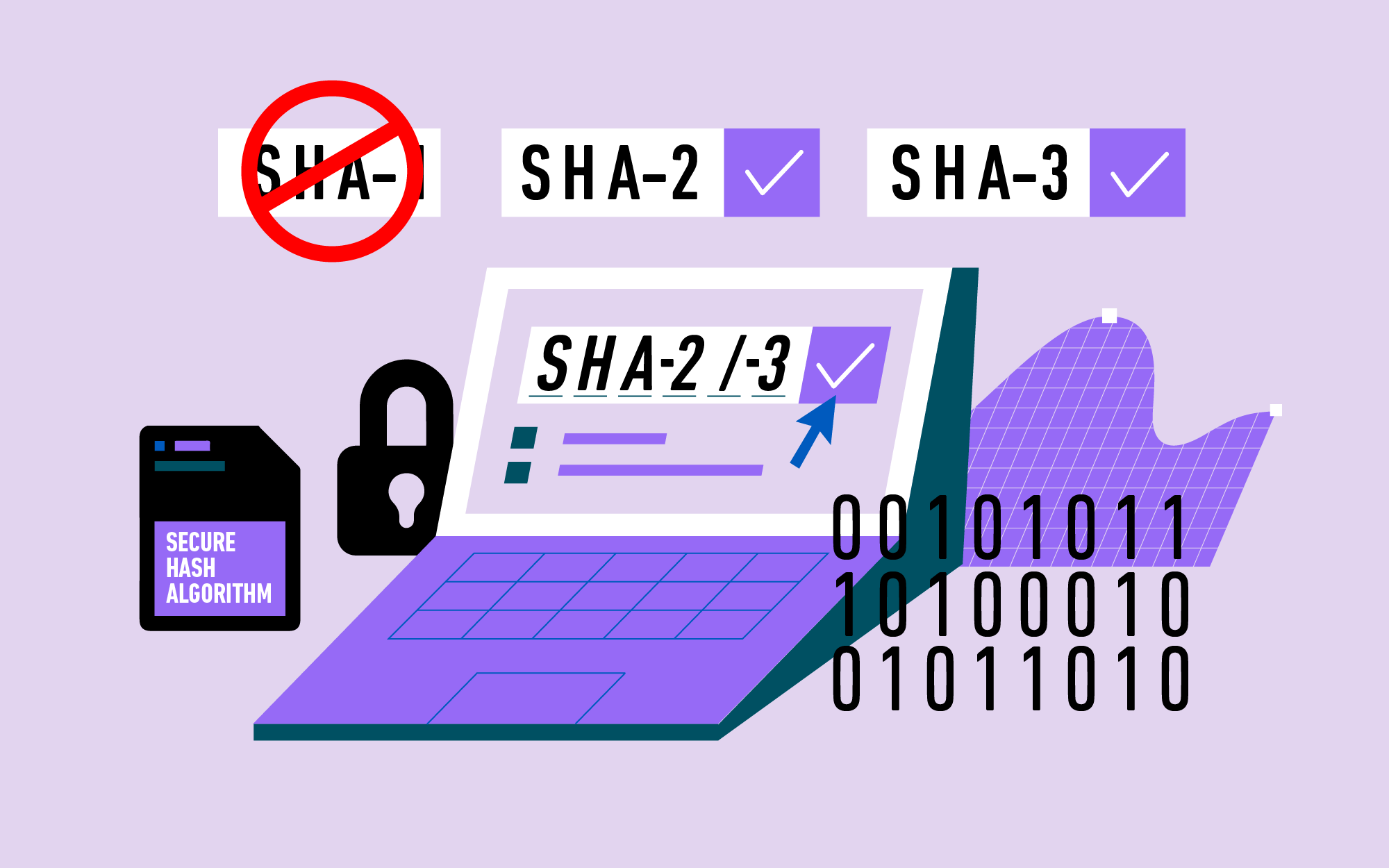
What is Secure Hash Algorithm (SHA)
Together, we foster a community that celebrates sacred heart’s mission of leading with courage, compassion, and commitment. An algorithm that consists of bitwise operations, modular additions, and compression functions. They differ in the word size
A secure hashing algorithm, or sha, changes data by creating a hash digest unique to each plaintext message
Sha is an acronym for secure hash algorithm, a family of cryptographic hash functions designed by the national security agency (nsa) This cryptographic hash function plays a critical role in ensuring the integrity and security of digital data. Sha is an important aspect of cryptographic algorithms as it guarantees integrity when it comes to information Sha1 and sha2 are the most commonly used hashing algorithms in security solutions, such as in ssl certificates and in digital signatures.
Secure hash algorithms, also known as sha, are a family of cryptographic functions designed to keep data secured It works by transforming the data using a hash function